Month: September 2015
-
Hyper-V Server 2012 R2 links
Sign up for a copy through Microsoft evaluations to get online video courses (example), virtual labs, white papers, … etc. Download ISO TechNet details TechNet forum TechNet blog
-

NTP tips
Checking your time against a reference NTP server w32tm /stripchart /computer:pool.ntp.org /samples:5 /dataonly Checking time across multiple systems using ‘psexec’ (from Sysinternals.com) psexec \\computer1,computer2,computer2 w32tm /stripchart /computer:pool.ntp.org /samples:5 /dataonly Setting the time services to use NTP and server NTP requests (for all AD servers). Step 1: W32tm /config /syncfromflags:manual /manualpeerlist:pool.ntp.org /reliable:yes /update W32tm /resync Step 2: [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\W32Time\Config] […]
-
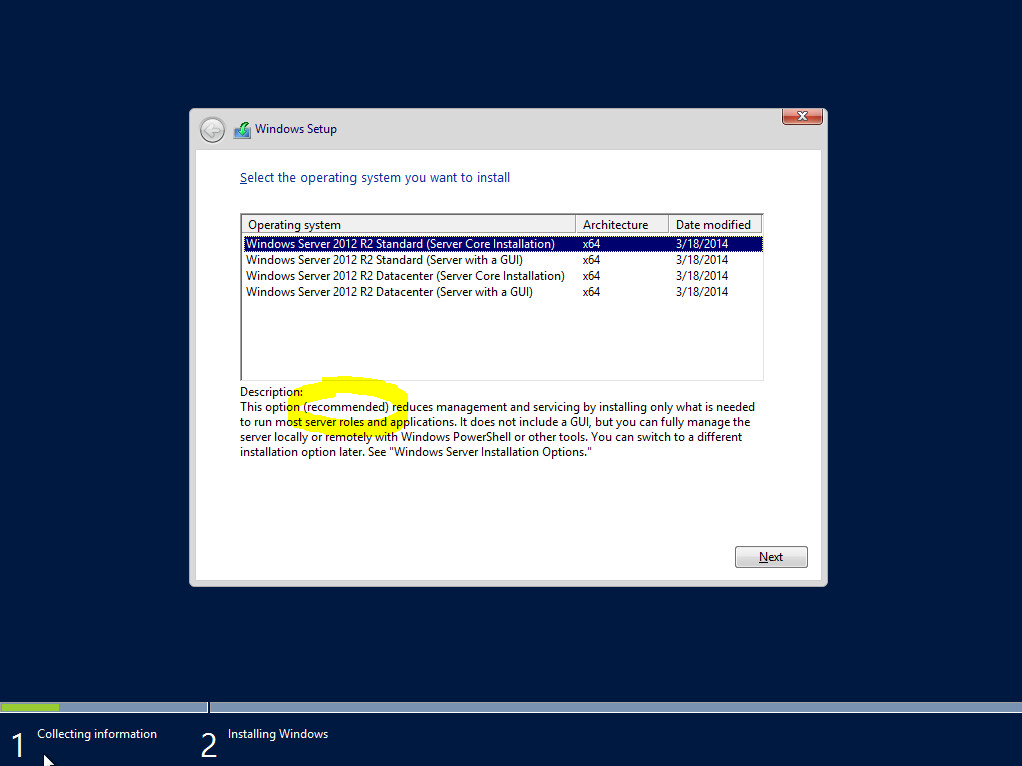
Core versus Full – Initial install quick stats
Created two VM’s with identical resources. On the first VM, Windows 2012 R2 Core Installation was chosen. On the second VM, Windows 2012 R2 Server with a GUI (Full) was chosen. After installation of both, I also ran updates on both until no more Windows updates were found. Here are the quick stats: Core has […]